If You’re Asking, “Is My Office Bugged?” You Need to Talk to
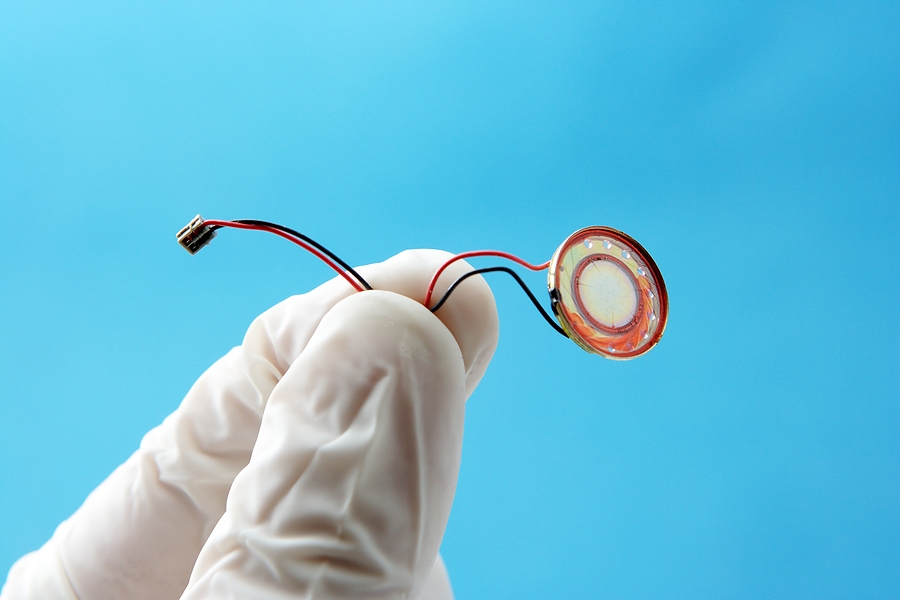
If a bad guy has access to your environment, they can plant a bug. The most common way a bad guy gains access to a home or business is through the “service technician ruse.” It isn’t just in the movies, but in real life, too. He dresses as a service technician and says he is there to perform some service. While he is on the premises, he installs the bug. You might be surprised how easy it is for bad guys to do that. Security processes need to be established in every business, because every home and business is vulnerable without them. It’s important to only allow in workers that you have called to come provide a service, for you to see identification and to [...]