Would a Bug Sweep of your Business Uncover any Spy Equipment?
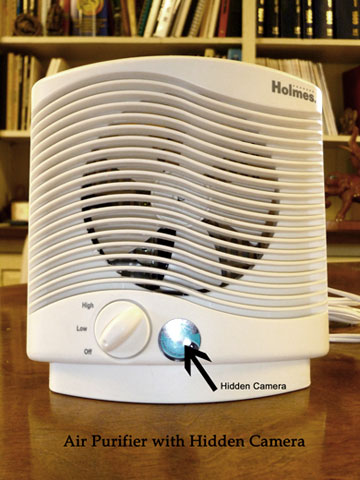
Just like an average citizen might ask who would want anything from them enough to take the time to engage in cell phone tapping, businesses across the nation might ask who would install eavesdropping devices or engage in electronic surveillance in their organizations. The answer is evident in a report from the National Counterintelligence Executive (NCIX). The report says that foreign spies account for economic espionage costing “the United States economy as much as $400 billion or more per year.” Some say that is grossly understated. Now that’s BIG BUSINESS – and not the kind U.S. business wants to see. Is your business being targeted? Corporate secrets and intellectual property are highly valued by competitors and years of research and development could be wiped out [...]